

1M European Market Email Database [2026]
1,000.00$ Original price was: 1,000.00$.99.00$Current price is: 99.00$.
Expanding to European markets? If so, you need to reach out to business contacts in those areas. With Emailproleads.com, you can find leads overseas easily by pulling this EUROPEAN MARKET EMAIL DATABASE contact directory, which is full of the emails, phone numbers, and contact information of local professionals.

Frequently Asked Questions about European Market Email Databases
What is a European Market Email Database Email Database?
A European Market Email Database Email Database is a collection of email addresses and contact information of potential customers and businesses within the European market. It is a valuable resource for businesses looking to expand their reach and target audiences in Europe.
How do the costs break down for a European Market Email Database Email Database?
The costs for a European Market Email Database Email Database may vary depending on the provider, the size of the database, and the level of customization required. Typically, the costs are influenced by the number of email addresses, additional contact information, and any specific targeting criteria desired by the business.
What value can businesses derive from a European Market Email Database Email Database?
European Market Email Databases provide businesses with a targeted and effective means of reaching potential customers in Europe. They can use the database to run email marketing campaigns, promote products or services, conduct market research, and establish a direct line of communication with their audience.
What are the top methods of Online Marketing with European Market Email Database Email Lists?
With a European Market Email Database Email List, businesses can employ various online marketing methods, such as email marketing campaigns, newsletter distribution, personalized offers, product updates, and targeted promotions. These methods can help businesses engage their European audience and drive conversions.
What industries benefit most from European Market Email Database Email Databases?
Various industries can benefit from European Market Email Databases, including e-commerce, travel and hospitality, technology, financial services, education, and more. Any business that aims to expand its reach and target customers in Europe can find value in utilizing such databases.
How can businesses customize their European Market Email Database Email Database?
Emailproleads European Market Email Databases usually offer customization options that allow businesses to target specific criteria, such as location, industry, job title, company size, and more. This level of customization helps businesses tailor their marketing efforts to the right audience and maximize their campaign’s effectiveness.
Why do businesses prefer Emailproleads European Market Email Database Email Databases?
Emailproleads European Market Email Databases are preferred by businesses due to their extensive and up-to-date collection of European email addresses and contact information. The databases are regularly maintained and verified, ensuring high deliverability rates and reliable data for successful marketing campaigns.
Is it legal to purchase European Market Email Database Email Databases?
The legality of purchasing European Market Email Databases depends on the data protection and privacy regulations in the respective European countries. It is essential for businesses to ensure they comply with all relevant laws and obtain explicit consent from individuals before sending marketing emails to them.
Is buying European Market Email Database Email Databases a good idea?
Buying European Market Email Databases can be a good idea for businesses seeking to expand their presence in Europe. However, it is crucial to choose a reputable provider and follow best practices to ensure the acquired data is used responsibly and ethically.
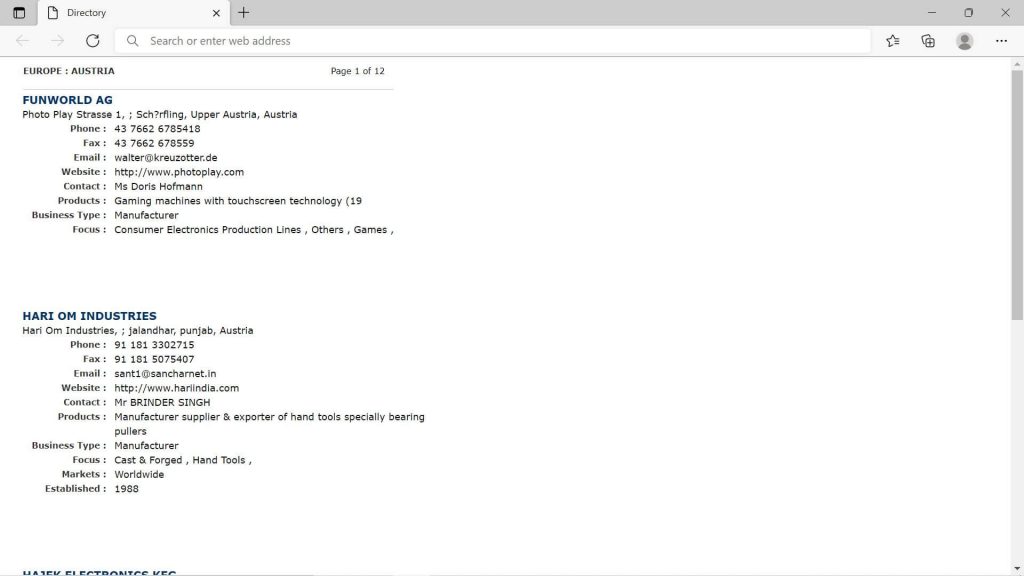
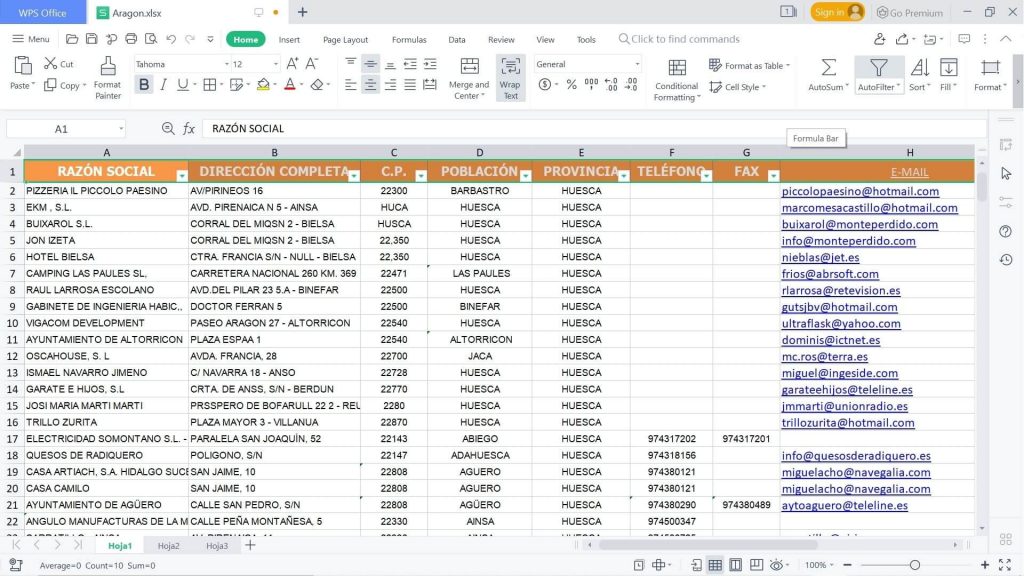
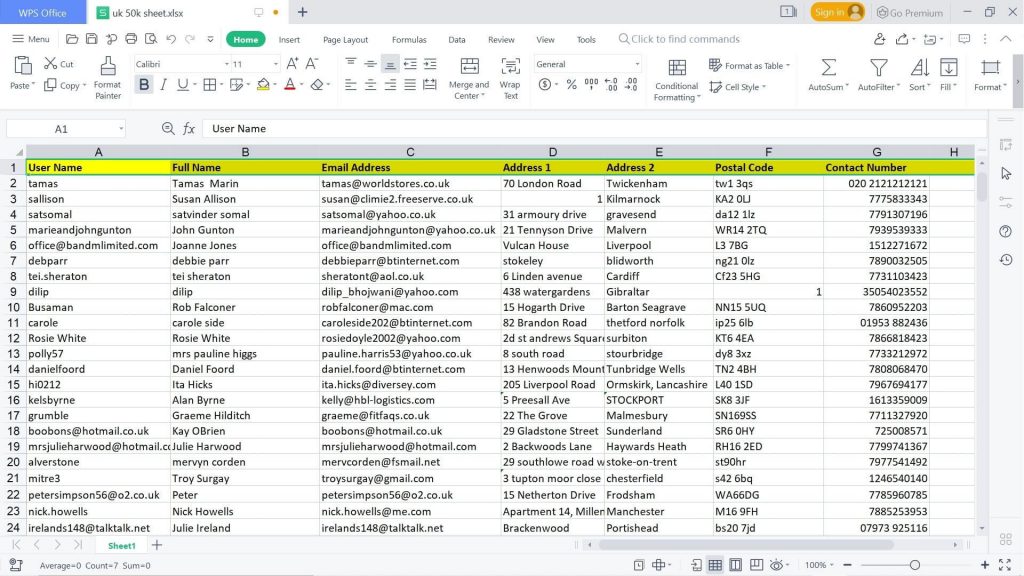
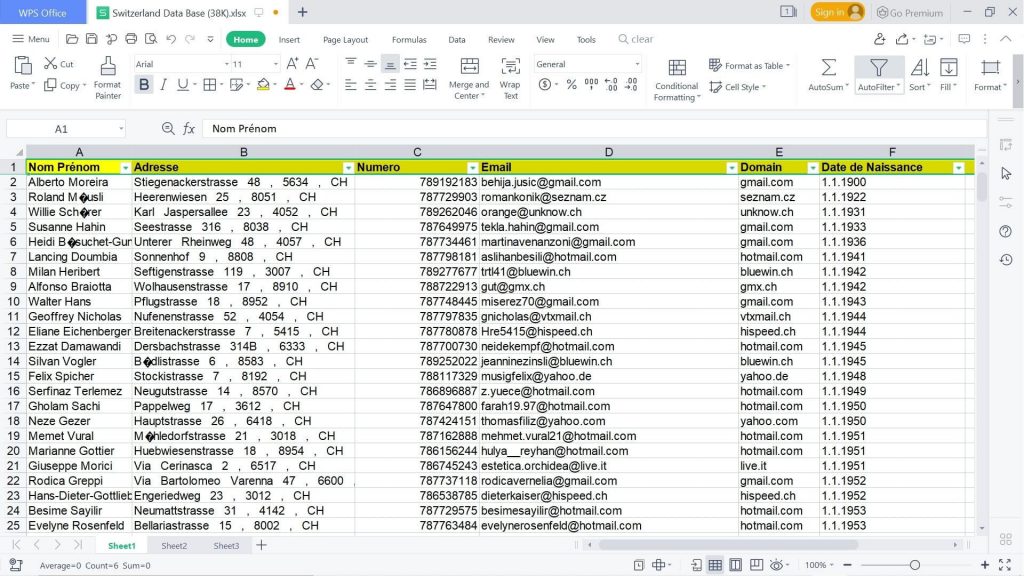
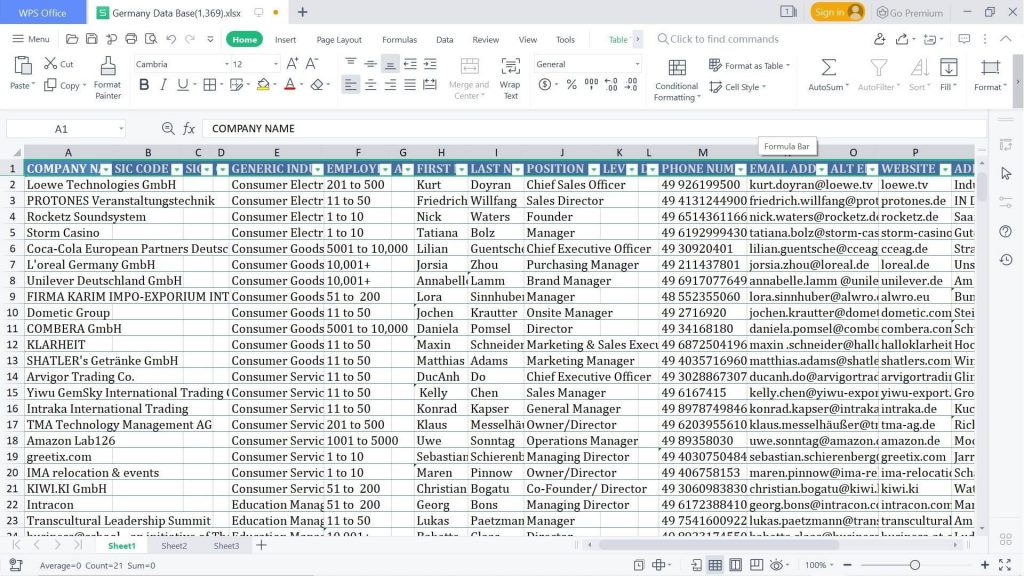
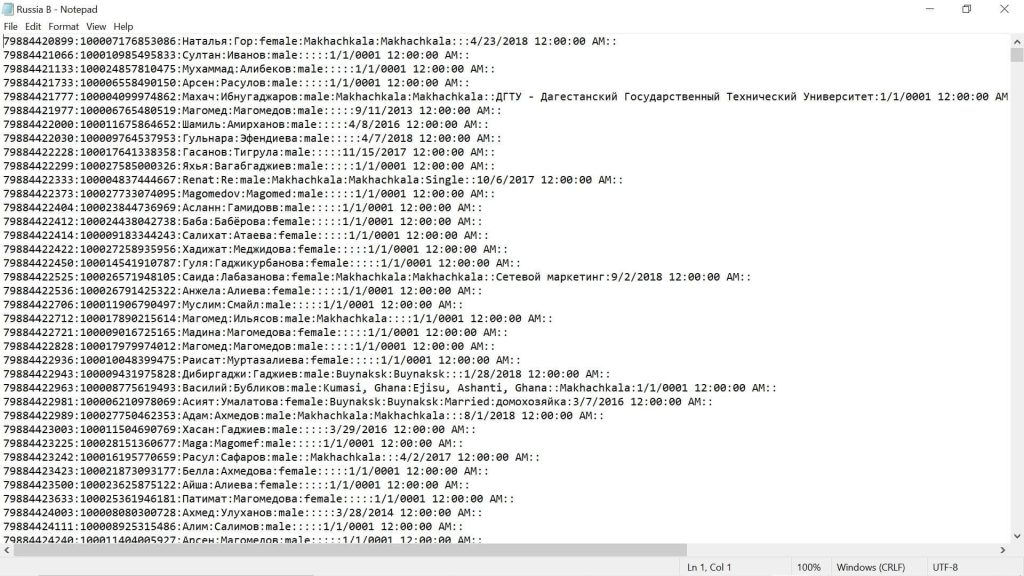
What information does a typical European Market Email Database Email Database include?
A typical European Market Email Database Email Database includes email addresses, names, postal addresses, phone numbers (if available), company details, industry classifications, and other relevant contact information of individuals and businesses within the European market.
Can I get targeted European Market Email Database Email Databases that include Phone Numbers?
Yes, many Emailproleads European Market Email Databases offer targeted lists that include phone numbers along with email addresses. This additional information can help businesses diversify their communication channels and improve customer engagement.
How often can I utilize the European Market Email Database Email Database?
Once you purchase a European Market Email Database Email Database, you can utilize it as per the terms and conditions set by the provider. Many providers offer unlimited usage, allowing businesses to conduct multiple marketing campaigns and stay connected with their European audience regularly.
How can I increase my email subscribers using European Market Email Database Email Lists?
To increase your email subscribers using European Market Email Database Email Lists, you can implement strategies like offering valuable content, exclusive deals, and discounts, optimizing sign-up forms on your website, conducting contests or giveaways, and leveraging social media to promote your email subscriptions. Additionally, sending personalized and relevant content to your subscribers can help retain and grow your email list.
2026 EUROPEAN MARKET EMAIL DATABASE
{1 MILLION lists}
Perhaps you hope to show your company’s products and services to global consumers and need to make valuable business contacts before jumping into the European market.
EUROPEAN MARKET EMAIL DATABASE
Perhaps you want to find better leads for your next business-to-business (B2B) marketing campaign.
EUROPEAN MARKET Email Lists
Or perhaps you simply want to network with the top professionals in Europe.
EUROPEAN MARKET Email Leads
No matter how you want to use this reliable list of accurate contact information, you can boost your sales and make better leads.
EUROPEAN MARKET Mailing Lists
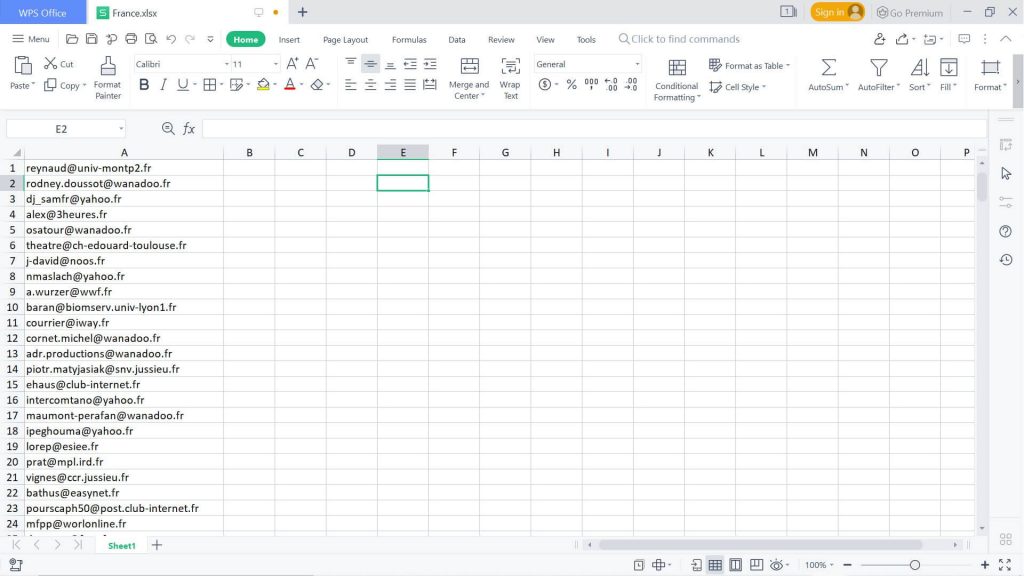
With this pre-made EUROPEAN MARKET EMAIL DATABASE list, which is ready for you to download now, you can find contacts in the following countries:
- Austria
- Belgium
- Czech Republic
- Denmark
- Finland
- France
- Germany
- Greece
- Hungary
- Ireland
- Italy
- Netherlands
- Norway
- Poland
- Portugal
- Spain
- Sweden
- Switzerland
- Turkey
EUROPEAN MARKET Email Address
With Emailproleads.com, it’s easier than ever to reach overseas audiences. You can reach out to business contacts in all of these countries and meet with the key influencers who can further your brand.
EUROPEAN MARKET Business Email Database
EUROPEAN MARKET Consumer Email Database
Today, within minutes, you can download this list, integrate it into your CRM, and start emailing, calling, and writing to these contacts. Pull it and expand your global reach to European markets today!
What is email marketing?

Improve Your Marketing with an European Email Database
Effective communication is essential to any business in today’s digital world. Email marketing is one of the most effective tools for this. Businesses can reach out to potential customers in Europe by leveraging an **European email list**. This will enhance their marketing efforts and drive sales.
What is the purpose of a European Email Database?
- European Email List is a targeted way to reach customers in certain regions. A well-curated database of emails can be a cornerstone in your marketing strategy, whether you want to expand your business into Germany, France or Spain. Here’s why:
- Targeted marketing: With an **European email list** you can send messages tailored to specific demographics and ensure that your marketing efforts are received by your audience.
Email marketing has a high return on investment. You can increase conversions by targeting the right audience and using relevant content.
Email marketing is a relatively cheap marketing channel compared to other channels. This allows businesses of any size to compete on an equal playing field.
Emails allow you to personalize messages and make your marketing campaigns more effective.
How To Use A European Email List For Maximum Impact
It’s important to use best practices in order to ensure that your campaign is both effective and compliant, such as with the GDPR.
- Segment your Audience Not all customers have the same needs. You can create highly-targeted campaigns by segmenting your list according to factors like location, interest, and buying behavior.
- Create compelling content: Your emails should contain relevant and engaging content that is valuable to your recipients. To increase engagement, use compelling subject lines, personal greetings, and clearly defined calls to action.
- Optimize Deliverability : Make sure your emails are delivered to the inbox. Use best practices, such as using a domain that is verified, avoid spammy language and include an opt-out button.
- Monitor and analyze performance: Track metrics like click-through rate, conversion rates, and open rates to better understand your campaign’s effectiveness. This data can be used to improve your email strategy and refine your strategy.
Value of an European Business Email Database
- European Business Email Database is of great value to B2B businesses. You can connect directly with key decision makers in your industry and foster relationships that could lead to long-term business partnerships.
- Reach decision makers: A European B2B Email database contains contact information for key decision-makers from various industries. You can then pitch your product or service directly to the people who are in charge of purchasing decisions.
Stay compliant: It is important to make sure that your emails comply with the GDPR and any other regulations relating to data protection. You can rest assured that a reputable provider of email databases will provide GDPR-compliant list, giving you peace and mind when you are reaching out to your potential clients.
In the world of B2B, networking is crucial. You can create a professional network by regularly communicating with the contacts in your contact database. This can lead to opportunities and collaborations.
Conclusion
- European email list is an excellent investment for companies looking to expand in the European market. A well-curated list of email addresses can help you reach your marketing goals, whether you are targeting businesses or consumers.
You can create email marketing campaigns which resonate with your target audience, increase engagement and improve your bottom line by following best practices.
Leverage the power of an European Email Database to enhance your marketing efforts. Start building relationships and driving sales to achieve your business goals.
This new content focuses on the strategic benefits of using a European Email Database, which makes it valuable and relevant to your audience. This should improve the SEO of your website and increase user engagement
Purchase also: France Email Database [2026]
| Plans | Starter Plan: 100,000 for $99, Growth Plan: 670,000 for $149, Enterprise Plan: 1,000,000 for $179 |
|---|
You must be logged in to post a review.
Related products
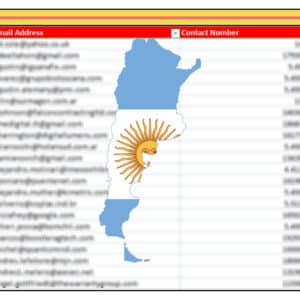
100k Argentina Email Database [2026]
100k Biotechnology Email Database [2026]
Biotechnology Email Database is an accurate, human-verified from Emailproleads.com contains all the contact details you require. Find people working in the biotech field in a matter of minutes after buying this directory ready to download. Locate bio technicians who have emails and contact details right now.

100k Hong Kong Email Database [2026]
100k Hungary Email Database [2026]
100K Philippines Email List & Database [2026 Updated]
150k Colombia Email Database [2026]
200k Kuwait Email Database [2026]
500k Saudi Arabia Email Database [2026]












Reviews
There are no reviews yet.