Colleges Universities Phone Number Database
The #1 site to find Colleges Universities Phone Number Database and accurate B2B & B2C Phone Number Database. Emailproleads.com provides verified contact information for people in your target industry. It has never been easier to purchase an Contact list with good information that will allow you to make real connections. These databases will help you make more sales and target your audience. You can buy pre-made mailing lists or build your marketing strategy with our online list-builder tool. Find new business contacts online today!
Just $199.00 for the entire Lists

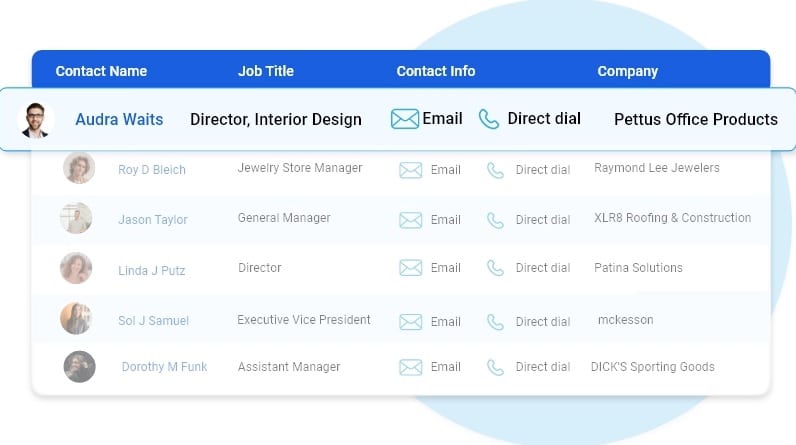
Customize your database with data segmentation
- Job Titles
- Job Function
- Company Size
- Revenue Size
- SIC Codes
- NAICS Codes
- Geographics
- Technology
- And more...

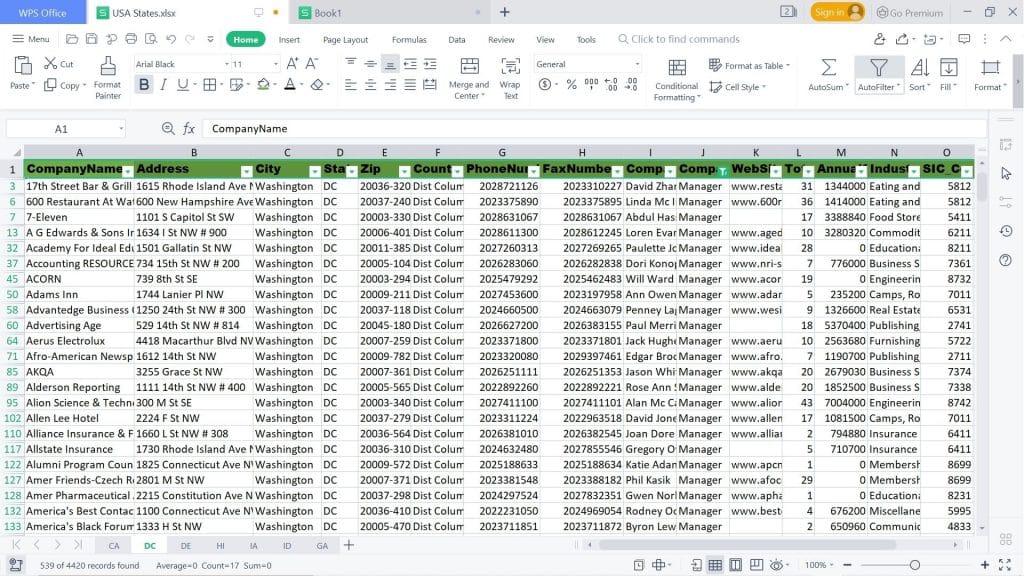
Free samples of Colleges Universities mobile number database
We provide free samples of our ready to use Colleges Universities contact Lists. Download the samples to verify the data before you make the purchase.
Human Verified Colleges Universities Mobile Number Lists
The data is subject to a seven-tier verification process, including artificial intelligence, manual quality control, and an opt-in process.
Best Colleges Universities contact number lists
Highlights of our Colleges Universities Contact Lists
First Name
Last Name
Phone Number
Address
City
State
County
Zip
Age
Income
Home Owner
Married
Property
Networth
Household
Cradit Rating
Dwelling Type
Political
Donor
Ethnicity
Language Spoken
Email
Latitude
Longitude
Timezone
Presence of children
Gender
DOB
Birth Date Occupation
Presence Of Credit Card
Investment Stock Securities
Investments Real Estate
Investing Finance Grouping
Investments Foreign
Investment Estimated
Residential Properties Owned
Traveler
Pets
Cats
Dogs
Health
Institution Contributor
Donates by Mail
Veteranin Household
Heavy Business
Travelers
High Tech Leader
Smoker
Mail Order Buyer
Online Purchasing Indicator
Environmental Issues Charitable Donation
International Aid Charitable Donation
Home Swimming Pool
Look at what our customers want to share





FAQ
Our email list is divided into three categories: regions, industries and job functions. Regional email can help businesses target consumers or businesses in specific areas. Colleges Universities Email Lists broken down by industry help optimize your advertising efforts. If you’re marketing to a niche buyer, then our email lists filtered by job function can be incredibly helpful.
Ethically-sourced and robust database of over 1 Billion+ unique email addresses
Our B2B and B2C data list covers over 100+ countries including APAC and EMEA with most sought after industries including Automotive, Banking & Financial services, Manufacturing, Technology, Telecommunications.
In general, once we’ve received your request for data, it takes 24 hours to first compile your specific data and you’ll receive the data within 24 hours of your initial order.
Our data standards are extremely high. We pride ourselves on providing 97% accurate Colleges Universities telephone number database, and we’ll provide you with replacement data for all information that doesn’t meet your standards our expectations.
We pride ourselves on providing customers with high quality data. Our Colleges Universities Email Database and mailing lists are updated semi-annually conforming to all requirements set by the Direct Marketing Association and comply with CAN-SPAM.
Colleges Universities cellular phone number list
Emailproleads provides Mobile Database to individuals or organizations for the sole purpose of promoting your business. In Digital Marketing. The mobile number database of Emailproleads helps to reach the highest level of business conversations.
Mobile number databases are a crucial marketing tool with many numbers from all over the globe. Since the arrival of smartphones, there has been an exponential rise in the number of buyers because technology has changed the way of marketing. Mobile number databases are essential for every retailer today in marketing and selling their goods and services. The world is now filled with mobiles that have internet connectivity across the globe.
Colleges Universities contact number lists
Now and again, we can see advertisements promoting the company. These ads result in the expansion of the company. It is possible to expand your marketing further using other services for Digital Marketing like Bulk SMS, Voice Calls, WhatsApp Marketing, etc.
Emailproleads checks every mobile number in the database using various strategies and techniques to ensure that buyers receive the most appropriate and relevant customer number and successfully meet their marketing goals and objectives.
This service assists you find your loyal customers keen to purchase your product. If you’d like to see your brand acknowledged by customers, using a database of mobile numbers is among the most effective ways to accomplish this.
What is the meaning of Phone Number Data?
A telephone number is a specific number that telecommunication firms assign to their customers, thus permitting them to communicate via an upgraded method of routing destination codes. Telecom companies give whole numbers within the limits of regional or national telephone numbering plans. With more than five billion users of mobile phones around the world, phone number information is now a gold mine for government and business operations.
What is the method of collecting the phone Number Data collected?
Having the number of current and potential customers and marketing professionals opens up a wealth of opportunities for lead generation and CRM. The presence of customer numbers is an excellent way to boost marketing campaigns as it allows marketers to interact with their target audience via rich multimedia and mobile messaging. Therefore, gathering phone number information is vital to any modern-day marketing strategy. The strategies consumers can use to collect data from phone numbers include:
* Adding contact forms on websites.
* Requests to be made for phone calls from customers.
* Use mobile keyword phrases for promotions to encourage prospective customers to contact you.
* Applying app updates prompts users to change their email details each time they sign in.
* Acquiring phone numbers that are already available information from third-party service companies with the information.
What are the main characteristics of the Phone Number Data?
One of the critical advantages of phone number data is that it is created to reveal the geographic location of mobile users because phone numbers contain particular strings specific to a region or country that show the user’s precise position. This is useful in targeted campaigns, mainly where marketers target a specific area that can target their marketing efforts.
To prevent duplicates and improve accessibility, the phone number information is typically stored in the E164 international format, which defines the essential characteristics of a recorded phone number. The specifications that are followed in this format are the number code for the country (CC) and an NDC, a country code (CC), a national destination code (NDC), and the subscriber number (SN).
What do you think of the phone Number Data used for?
The possibilities that can be made possible by the phone number information are endless. The availability of a phone number database means that companies worldwide can market their products directly to prospective customers without using third-party companies.
Because phone numbers are region – and country-specific and country-specific, data from phone numbers gives marketers a comprehensive view of the scope of marketing campaigns, which helps them decide on the best areas they should focus their time and resources on. Also, governments use the data from mobile numbers to study people’s mobility, geographic subdivisions, urban planning, help with development plans, and security concerns such as KYC.
How can an individual determine the validity of Phone Number Data?
In determining the quality of the phone number information, users should be aware of the fundamental quality aspects of analysis. These are:
Completeness. All info about phone numbers within the database must be correct.
Accuracy. This measure reflects how well the data identifies the individual described within the actual world.
Consistency. This indicates how well the data provider follows the rules to facilitate data retrieval.
Accessibility. The phone number database should be accessible where the data is organized to allow easy navigation and immediate commercial use.

Where can I purchase Phone Number Data?
The Data Providers and Vendors listed in Datarade provide Phone Number Data products and examples. Most popular products for Phone Number Data and data sets available on our platform include China B2B phone number – Chinese businesses by Octobot, IPQS Phone Number Validation and Reputation through IPQualityScore (IPQS), and B2B Contact Direct Dial/Cell Phone Number Direct Dial and mobile numbers for cold calling Real-time verified contact email and Phone Number by Lead for business.
How do I get my phone Number Data?
You can find phone number data from Emailproleads.
What are data types similar that are similar to Phone Number Data?
Telephone Number Data is comparable with Address Data; Email Address Data, MAID Hashed Email Data, Identification Linkage Data, and Household-Level Identity Data. These categories of data are typically employed to aid in Identity Resolution and Data Onboarding.
Which are your most popular uses for Phone Number Data?
The top uses that involve Phone Number Data are Identity Resolution, Data Onboarding, and Direct Marketing.
Let’s say you’re running a business selling strategy that demands you to connect with the maximum number of people you can. If your job is laid off for you, it can often be challenging to determine what to do. First, you should create your list of prospective customers and then save your call data in an electronic database.
Colleges Universities Telephone Number Lists
Though you might believe that working with lists of telephone numbers and storing them in databases is all you need to launch a cold calling campaign, it’s not the case. Since a telephone number database could contain thousands or millions of leads, along with important data points about each potential customer, It is essential to adhere to the best practices for a Database of telephone numbers. Methods to avoid becoming overwhelmed or losing important data.
To build a phone number database that delivers outcomes, you must start on the right starting point. It is possible to do this by purchasing lists of sales leads from a reliable, dependable company like ours. It’s equally important to have the right tools to allow your team to contact the most people possible.
In addition to high-quality telephone marketing lists, we provide advice on the best techniques for targeting databases and dialer software that can make lead generation more efficient and less expensive over time. Our customer service representatives are ready to assist you.
Colleges Universities Telephone Number Database Best Practices
After you’ve established the basis for success by acquiring high-quality lead lists and implementing dialers that can boost how many calls your team receives by up to 400 percent, you’re ready to become familiar with best practices for your industry. By adhering to a list of phones and best database practices, you’ll dramatically improve the odds that your team will succeed in the short and long term.
Colleges Universities cell phone number list
Here are the best techniques for telemarketing databases that you should consider a priority to observe.
Get Organized
A well-organized Colleges Universities mobile phone directory includes contacts organized according to phone country, postal, area, city, and province. By narrowing your calls to only one of the criteria, it is possible to incorporate new business information into your list, then sort and retarget top leads.
Colleges Universities mobile number list
Create a strategy to manage your phone lists. Naturally, your organizational plan must be based on the purpose of your cold-calling campaign. Your business’s goals will affect the traits your most promising prospects have. Make a profile of the most appealing candidate based on the plans for your marketing campaign. Make sure you make your leads list to ensure that the candidates who best meet your ideal profile of a prospect are first on your list of leads. List.
Colleges Universities cellular phone number list
Determine Who Has Access to and edit your database
Your phone number list doesn’t only represent an investment in money but also a resource that your team can use to increase sales. Although your phone number list is essential because you bought it, it’s also advantageous due to the possibility that it can improve your bottom line. In this regard, you should think carefully about who has access to and control your database.
It is generally recommended to restrict the number of users who have access to your database to only those who use it to communicate with potential customers to achieve your campaign’s goals. If an individual is not active with your marketing campaign, then there’s no reason for them to gain access to your telephone number database.
It’s also advisable to restrict access to the database you have created; it’s best to allow editing privileges to people who require them. This generally means that you only give editing rights to agents that will be conducting cold calls. It will be necessary to modify the database to make changes to records and notes that could aid in subsequent calls.
Colleges Universities phone number database
Create Your Database
Databases are knowledge centers that store information for sales personnel. They are vital to gain knowledge and share it with your sales staff. Even if it’s just to keep call notes, callback databases can help your sales team to achieve maximum value and benefit from lists of telemarketing calls.
As time passes, your phone number list will likely expand and include more contact numbers and information on your customers. When you get recommendations from your current prospects or purchase leads lists, or either, it’s essential to grow the size of your database to include as much data as you can to assist you in achieving your goals for the business in the near and far future and at every step in between.
4. Keep Your Database
Although you want your database to expand with time, you do not want it to contain obsolete or ineffective details. To keep your database from overloading with useless information, it’s essential to maintain it regularly, including removing old records and updating your prospective customers with their contact details.
One of the most effective ways to ensure your database is to ensure that it doesn’t contain numbers listed on the Do Not Call list. If you make a call to an address that is listed on a Do Not List, you could result in your business spending lots of money, perhaps even millions. With the free tools available online, think about scrubbing all your data against the Do Not Call registry at least twice yearly.
If you’ve learned the basics of a telephone list and best practices for database management, you can contact
Colleges Universities mobile number database
Emailproleads.com now to receive the top-quality leads lists you need within your database. Colleges Universities phone number database free download
Today, download the mobile phone/cell numbers directory of all cities and states based on the network or operator. The database of mobile numbers is an excellent resource for advertising and bulk SMS, targeting specific regions of people, electoral campaigns, or other campaigns. Before you use these numbers, verify the ” Do Not Disturb” status in conjunction with TRAI. If it is activated, it is not permitted to use these numbers to promote your business.
Buy Colleges Universities Phone Number Database
It’s the quickest method of building an extensive list of phone numbers for your potential customers. Pay a fixed sum (per list, contact, country, or industry) and get every mobile number you paid for and have in your possession. You can then utilize them several times to reach out to customers to convince them to purchase their products or products. Doesn’t that sound great?
Colleges Universities phone number listing
Although it may seem like the fastest method of building a list of numbers, it’s not the case. There are a lot of risks associated with purchasing mobile marketing lists which won’t generate sales:
They’re not well-targeted. It’s impossible to be sure that every person on the bought phone lists will pay attention to the emails you’ve sent or your company worldwide.
Colleges Universities contact number lists
It will help if you trust someone completely. When you purchase a mobile phone list, you’ll need to be able to trust your seller about how active the numbers are. It’s possible that the majority of the phone numbers you’re buying are not current or relevant.
BLOG
College Universities Phone Number Database
The growth of Bitcoin is quite impressive when you look at all the other ventures which failed to accomplish what it can do. Bitcoin is a notable innovation such as the block chain, and an uncentralized model that allows transactions between users. It offers a practical but not perfect level of privacy for the users. In Chapter 6, we’ll go over an in-depth look at privacy in Bitcoin.
In one way, it’s weaker than the robust anonymity of DigiCash however in another way it’s more secure. This is because in DigiCash the only thing that was protected was the users who were sending the money who kept their identities private, it wasn’t the sellers. Bitcoin offers both senders and buyers (whether customers or merchants) the same degree of privacy.

College Universities phone number database
Let me close with a few lessons that we can draw from Bitcoin using the lenses of the other systems we’ve studied. First, don’t abandon a problem. Even if people have failed for 20 years when it came to developing digital money doesn’t mean that there’s no system in place that can work. The second thing is to be prepared to compromise. If you’re seeking absolute anonymity or a perfect decentralization, you’ll probably have to improve some of the areas you’ve designed. Bitcoin is, looking back appears to have made good choices. It reduces the anonymity of its users a bit, and demands that users be connected and online the peer-to-peer network. However, it turned out to be a good choice for users. Buy college universities phone number database.
One final point is that success is achieved by numbers. Bitcoin has been able to build an enthusiastic community of users and developers who were willing to contribute to this open source technology. This is a distinct approach to earlier attempts to create digital currency that were created by a corporation with the sole advocates to the system being people working for the firm. The current success of Bitcoin is due to the thriving community of supporters who promoted the technology, enlisted people to use it, and pushed merchants to accept it.
Introduction to Cryptography & Cryptocurrencies
Every currency requires a way to regulate supply and enforce different security features to stop
cheating. When it comes to fiat currencies organisations such as central banks manage the amount of money they have and then increase the amount of money available.
security features that prevent counterfeiting of physical currency. These security features make it harder for an attacker. Buy college universities phone number database.
But they can’t make it unattainable to steal. In the end, law enforcement is crucial to protect
stopping people from violating regulations of our system.
Additionally, cryptocurrencies must be protected by security measures to prevent users from altering the state of the system, or from equivocating. That is, giving contradicting statements to various people. If Alice claims to Bob that she has paid him a digital currency for instance she shouldn’t be in a position to convince Carol that she actually paid the same amount. However, unlike fiat currencies the security requirements of cryptocurrencies must be enforced solely technologically and without the need for an authority central to the system. Buy college universities phone number database.
The word “cryptography” means that cryptocurrency makes usage of cryptography. Cryptography is a method of securely coding the principles of a cryptocurrency system within the system itself. It can be used to stop tampering and equivocation and also to encode the rules of the creating new units of currency into a mathematical process. To fully comprehend the cryptocurrencies, we’ll need to understand the cryptographic principles they are based on.
College Universities phone number and address database
The field of cryptography is an extensive academic field that employs a variety of sophisticated mathematical techniques which are notoriously nebulous and hard to grasp.

College Universities phone number and address database
However, Bitcoin does not rely on the use of a few simple and well-known cryptographic structures. This chapter will examine cryptographic hashes as well as digital signatures, two fundamentals which prove efficient in creating cryptographic currencies. The next chapters will cover more complex cryptographic schemes, like zero-knowledge proofs which are utilized in the proposed extensions and changes to Bitcoin.
When we’ve taken in the important cryptographic natives, we’ll examine a portion of the manners by which those are utilized to fabricate digital currencies. We’ll finish this section for certain instances of basic digital currencies that outline a portion of the plan difficulties that we really want to manage.
Cryptographic Hash Functions
A cryptographic hash function is the first cryptographic primitive we need to understand. It is a mathematical function that has three properties.
It can input any string of any length. Buy college universities phone number and address database.
It produces an output of fixed size. We will assume that the output size is 256 bits to make the discussion concrete. Our discussion is valid for any output size, as long as it’s sufficient.
It is efficient computable. This means that you can find the output of the hash function for any input string in a reasonable time. Technically speaking, the time required to compute an n-bit string’s hash should be O(n).
These properties are a general hash function that can be used to create a data structure, such as a hashtable. We will be focusing exclusively on cryptographichash function. For a hash function to be cryptographically secure, we’re going to require that it has the following three additional properties: (1) collision-resistance, (2) hiding, (3) puzzle-friendliness. Buy college universities phone number and address database.
To understand why it is useful to have a function behave this way, we will examine each property more closely. A cryptography student should be aware of the differences in how this book treats hash functions. Although puzzle-friendliness is not required for cryptographic hash function, it will prove useful for cryptocurrency.
Property 1: Collision-resistance.The first property that we need from a cryptographic hash function is that it’s collision-resistant. When two inputs produce the exact same output, a collision is occurring. A hash function H (.) iscollision-resistant if nobody can find a collision. Formally:
Collision-resistance: Ahash functionHis said to be collision resistant if it is infeasible to findtwo values, xand y,such that xy,yet H(x)=H(y). Buy college universities phone number and address database.
Although we stated that nobody could find a collision, we didn’t say that there aren’t any collisions. We know that collisions exist and can prove it with a simple counting argument. The input space for the hash function includes all strings of any length, while the output space only contains strings of a fixed length. The input space is larger that the output space, and the input space can be infinite while the output spaces are finite, so there must be input strings which map to the same output string. According to the Pigeonhole Principle, there will always be many inputs that map directly to an output. Buy college universities phone number and address database.
If we randomly select 2 + 1, there is a 99.8% chance of at least two of them colliding. We can only examine the square root of the possible outputs to find a collision. This is a phenomenon of probability called the birthday paradox.
This is a very general, but not practical, algorithm for finding collisions for any hash function. The more difficult question is, is there another method that can be used to locate a collision for a specific hash function? The generic collision detection algorithm may not be practical to use, but there might be another algorithm that can find a collision for a particular hash function. Buy college universities phone number and address database.
Application: Message digests. Now that we understand collision-resistance, the next question is: What does collision-resistance serve? Let’s look at one example: If two inputs x and yto a collision resistant hash function Hare are different, it is safe to assume their hashes H (x)and H (y)are different. However, if they knew an xand an ythat were both different but shared the same hash, this would contradict our assumption that His collision resistance.
College Universities phone number and email database
This argument allows us use hash outputs to create message digests. SecureBox is an online file storage system that authenticates users and allows them to upload files. Let’s say Alice uploads a large file and wants to verify that it is the same file that she uploaded. You can do this by saving the entire file locally and comparing it with the one she downloaded. Although this is possible, it defeats the purpose behind uploading it. Alice can use the local copy if she needs access to the file to verify its integrity.

College Universities phone number and email database
This problem can be solved elegantly and efficiently by using collision-free hashes. Alice only needs to know the hash of her original file. She later downloads the file from SecureBox and computes the hash. Then she compares it with the one she had previously saved. If they match, she can confirm that it is the file she uploaded. However, if the hashes differ, Alice can conclude that it was altered. Remembering the hash thus allows her to detect accidentalcorruption of the file during transmission or on SecureBox’s servers, but also intentionalmodification of the file by the server. These guarantees are essential to cryptography’s ability to detect malicious behavior from other entities.
The hash is a fixed-length digest or unambiguous summary of a message. This allows us to quickly recall things we have seen and help us recognize them again. The entire file could have been gigabytes in size, but the hash has a fixed length of 256 bits for our hash function. This significantly reduces the storage requirements. We’ll be discussing applications where a hash can be useful as a message digest later in this chapter. Buy college universities phone number and email database.
Property 2: Hiding This property cannot be true in its stated form. Let’s take an example. We will flip a coin. If the result of the coin flip was head, we will announce the hash string “heads”. If the result of the coin flip was heads, we’ll announce the hash for the string “heads”.
Then, we ask an adversary (who didn’t see this coin flip but saw the hash output) to determine the string that was hashed. We’ll soon understand why this game is so popular. They would then simply compute the hash for the string “heads” as well as the hash for the string “tails” to see which one was given. In just a few steps they can determine what the input was.
Because there were only two possible values for x, the adversary was able guess the string. It was also easy to try both. To be able achieve the hiding property, it must be clear that there is no value of x which is especially likely. This means that xmust be selected from a set that is in some way very distributed. This method of trying to find a few likely values of x will not work if xis selected from such a set. Buy college universities phone number and email database.
The big question is, can we attain the hiding property if the values we desire are not from a spread-out group like in our “heads” and “tails” experiments? The answer is yes, Perhaps we can conceal an input that isn’t spread out by concatenating with another input that has been spread out.
Information-theory uses min-entropy to measure how predictable an outcome is.
Min-entropy refers to the intuition that the distribution (i.e. random variable) is extremely spread out. This means that we can’t sample from the distribution and find any particular value.
It’s very likely that it will happen. For example, let’s say that ris is chosen uniformly among all the strings. Buy college universities phone number and email database.
256
If the length of a string is 256 bits, it was selected with probability 1/2, which is an infinisimally small value.
Application: Commitments. Now let’s examine an application of hiding property. We are referring to a “commitment” in particular. This is the digital equivalent of taking a value and sealing it in an envelope. Then, we will examine how to apply the hiding property. You have committed to the contents of the envelope by doing this. You haven’t yet opened the envelope, so even though it’s your commitment to a certain value, it remains secret from others. You can later open the envelope to reveal the value you have committed to. Buy college universities phone number and email database.
First, generate a random nuce to use in a commitment scheme. The commit function is then applied to the nonce along with msg (the value being committed too), and the commitment com is published. This stage is similar to putting the sealed envelope on a table. If we wish to reveal the value they have committed to previously, we will publish the random nonce we used to create the commitment and the message,msg. Now, anyone can verify that msg was the message that was committed to earlier. This is similar to opening the envelope.
College Universities phone number and email lists
It is crucial that every time you commit to a value it is chosen a random nonce value.
These two security properties mean that algorithms behave just like opening and sealing an envelope. First, a person looking at an envelope won’t be able to figure out the message if com is present. It’s also binding.

College Universities phone number and email lists
This means that you cannot change your mind after you have committed to the contents of the envelope. It’s impossible to find two messages. You can’t commit to one message and later claim you have committed to the other.
How do we determine if these properties are true? Before we can answer that question, we must discuss how we will actually implement a commitment program. This can be done using a cryptographic haveh function. Take a look at the following commitment scheme.
To commit to a message we generate a random nonce of 256 bits. Next, we combine the nonce with the message to generate a hash and return the commited value. Someone will then compute the same hash of nonce that they received concatenated to the message. They will also check if that is equal to the commitment they saw. Buy college universities phone number and email lists online.
Let’s take a look at the properties we need for our commitment schemes.
The commitments hiding property is precisely what we needed for our hash functions. If key was chosen randomly as a 256-bit value, then the hiding property states that it is impossible to recover the message from hash output if we hash keyand the message. It turns out that the binding property can be implimented by1 the collision-resistant property in the underlying hash functions.
This means that if He has a collision-resistant and hiding hash function, the commitment scheme will work in that it will have all the security properties.
Property 3: Puzzle friendliness. We will need the third security property from hash functions to be puzzle-friendly. This property is quite complex. First, we will explain the technical requirements for this property and then provide an application to show why this property is so useful. Buy college universities phone number and email lists online.
This means that it is very difficult to find another value to match the target if the input is selected in a random way.
Application: Search puzzle. Now let’s look at an application that illustrates this property’s usefulness. This application will build a search puzzle. It is a mathematical problem that requires us to search a large space to find the answer. A search puzzle is not easy to solve. This means that there is no other way to find the solution than by searching large spaces. The opposite is not true.
Search puzzle. Search puzzles consist of
A hash function, H.
A value, id (which we refer to as the puzzle-ID), is a value that was chosen from a high min entropy distribution
A target set Y
This intuition states that H can accept any 2nvalues if it has an output of n bits. Buy college universities phone number and email lists online. The input must be found so that the output falls within Y. This set is usually much smaller than all other outputs. How difficult the puzzle is will depend on how large Y is. The puzzle will be trivial if it has all the n-bit strings, but the one element puzzle will be the most difficult. There are no shortcuts because the puzzle ID has high min-entropy. However, cheating could be done if the ID had a certain value. For example, pre-computed solutions to the puzzle using that ID.
Puzzle-friendly means that a search puzzle can be solved in any way that is possible. This is true even if the puzzle-IDs are generated in an appropriately random manner. This idea will be used later in our discussion about Bitcoin mining.
College Universities phone number and email datas
SHA-256. We have discussed three properties and one application for hash functions. Let’s now discuss one particular hash function we will use in this book. There are many hash functions, but this one is the most popular and widely used. It is called SHA-256.
Remember that our hash functions must work with inputs of an arbitrary length. As long as we are able to build a hash functions that work on inputs of fixed length, there is a generic way to make it work on inputs of arbitrary length. This is the Merkle-Damgard transformation. This method is used by SHA-256, which is just one of many commonly-used hash functions. Common terminology refers to the compression function, which is a fixed-length collision-resistant hash functions. It has been shown that the overall hash function will also be collision resistant if it is collision-resistant.

College Universities phone number and email datas
It is very simple to use the Merkle-Damgard transformation. The Merkle-Damgard transform is very simple. The input length of the compression function will be (m-n+ n=m). We use an Initialization Vector instead for the first block. This number is used every time the hash function is called. In practice, you can simply look it up in a standard document. You return the output of the last block.
SHA-256 uses a compression algorithm that accepts 768-bit inputs and produces 256-bit outputs. Block size is 512 bits. For a graphic representation of how SHA-256 works, see Figure 1.3.
We have already discussed cryptographic hash function, hash functions that are cryptographic functions with special properties and their applications. Now we will discuss a particular hash function that is used in Bitcoin. We’ll be discussing how to use hash functions in order to create more complex data structures for distributed systems such as Bitcoin.
Sidebar: Modeling hash functions. Hash functions are the Swiss Army Knife of cryptography. They can be used in an amazing variety of applications. This versatility also means that different applications will require different properties for hash functions in order to guarantee security. It is notoriously difficult to identify the properties of hash functions that will provide provable security for all applications. Buy college universities phone number and email datas online.
We’ve chosen three properties that are critical to how hash functions work in Bitcoin and other cryptocurrency. These properties may not be necessary for all uses of hash functions. As we’ll see, Bitcoin mining is not the only area where puzzle-friendliness can be important.
Secure systems designers often give up and create model hash functions, functions that produce an independent random value for each input. Cryptography is still a controversial area. It doesn’t matter what your position is on the issue, it is important to think about ways to decrease the security properties we want in our applications. This can be useful intellectual exercise for building secure system. This chapter is intended to teach you this skill. Buy college universities phone number and email datas online.
Data Structures and Hash Pointers
This section will discuss hash pointsers and their applications. A hash pointer can be a data structure that is useful in many of these systems. A hash pointer simply points to the location of information, along with a cryptographic hash. A regular pointer allows you to retrieve the information. However, a hash-pointer can also be used to verify that the information has not changed. Buy college universities phone number and email datas online.
You can create all sorts of data structures using hash pointers. We can intuitively take a data structure such as a binary search tree or linked list and use hash pointers to implement it.
Block chain. In Figure 1.5, we created a linked list with hash pointers. This data structure will be called a block-chain. Unlike a regular linked listing that has a series blocks, each block contains data and a pointer at the previous block. In a block-chain, the block pointer to the block before it is deleted will be replaced by a hash key. Each block contains not only the value of the block before it, but also a digest that shows us the current value. This allows us to confirm that the value hasn’t changed. The head of the list is simply a regular hash-pointer that points at the most recent data block.
College Universities contact number lists
One use case for a blockchain is a tamper evident log. This means that we want to create a log data structure which stores lots of data and allows us add data to the log. We will detect if someone alters the data in the log.

College Universities contact number lists
Let’s look at what happens when an adversary tries to alter data in the middle of a block chain. This will help us understand why block chains have this tamper evident property. The adversary wants to do this in a way that anyone who only knows the hash pointer at block chain’s head won’t be able detect the tampering. The adversary alters the data in block k. This means that the block k+1 hash, which is a hash for the entire block, will not match up.
Because the hash function is non-coincidence resistant, statistically we can guarantee that the new hash won’t match the altered content. So we can detect inconsistencies between the block k data and the block k+1 hash pointer. The adversary could continue trying to cover this up by changing the hash of the next block. This strategy can be continued by the adversary, but it will not work once he reaches top of the list. The adversary can’t change any block as long as the hash pointer is stored at the top of the list. Buy college universities contact number lists online.
This means that the adversary will have to alter the hash pointers back to the beginning if he wants to tamper any data in the entire chain. He won’t have the ability to alter the head of the list, so he will eventually run into a roadblock. It turns out that just by remembering one hash pointer, all we have is a tamper evident hash of the entire list. This block chain can be used to build as many blocks as you want. We will refer back to the genesis block, which is the block at the start of the list.
It may be obvious that block chain construction looks very similar to Merkle-Damgard construction, which we discussed in the previous section. They are very similar and both have the same security argument.
Merkle trees. Another useful data structure we can create using hash pointsers is the binary tree. After Ralph Merkle, a Merkle tree is a binary tree that uses hash pointers. Let’s say we have data blocks. These blocks are the leaves of our tree. These data blocks are divided into two pairs and, for each pair of blocks, we create a data structure with two hash pointsers. These data structures form the next level of the tree. These data structures are then grouped into two groups and, for each pair of pairs, we create a new data format that includes the hash of each. Continue doing so until you reach the root of your tree, a single block. Buy college universities contact number lists online.
We still remember the hash pointer at its head. Now we can traverse the hash pointsers to any point on the list. This allows us to verify that the data isn’t being altered. Just like with the block chain, an adversary can tamper at a data block at the bottom, which will cause the hash pointser one level higher to not match. Even if he continues to do this, the change will eventually spread to the top tree where he will be unable to alter the hash keyer we have stored. Any attempt to alter any piece of data can be detected by simply looking at the hash key at the top. Buy college universities contact number lists online.
Merkle trees allow for proof of membership. Let’s say someone needs to prove that a particular data block is a member the Merkle Tree. We remember the root, as usual. They will then need to show us the data block and the blocks that connect it to the root. The rest of the tree can be ignored as the blocks along this path will suffice to verify that the hashes have been verified all the way to the root. This is illustrated in Figure 1.8.
Only log(n), if there are nnodes within the tree, need to be shown. Each step only requires us to compute the hash for the child block. It takes approximately log(n)time to verify. Even though the Merkle tree has a large number of blocks we can still prove membership within a short time. Verification therefore takes place in a time and space logarithmic to the number of nodes within the tree. Buy college universities contact number lists online.
A Merkle tree that is sorted is a Merkle tree in which we take the blocks from the bottom and sort them according to an ordering function. This could be an alphabetical, lexicographical, or numerical ordering, or any other type of agreed upon order.
College Universities mobile number lists
A Merkle tree sorted in logarithmic order can be used to prove non-membership. This means that we can prove that a block is not part of the Merkle tree. The way to do this is to show a path to an item just before the item in question and then the path to the one that is just after it. This is a sign that the item in question has been excluded if they are adjacent in the tree. It would have to be placed between the two items, but since they are consecutive, there is no space between them.

College Universities mobile number lists
Although we’ve already discussed the use of hash pointsers in binary trees and linked lists, more generally speaking, we can use them in any pointer-based data format as long as it doesn’t contain cycles. We won’t be capable of matching all the hashes if there are cycles within the data structure. You can begin near the leaves or the things without pointers, then compute the hashes from those and work back to the beginning of an acyclic structure. In a structure that is based on cycles, we cannot start from the end and then compute back.
Another example is to use hash pointers to build a directed-acyclic graph. We’ll also be able verify the membership of that graph with great efficiency. It will also be very easy to compute. This is how you can use hash pointers to compute. It’s a common trick that you’ll find time and again within the context of distributed data structures as well as the algorithms we will discuss later in this chapter. Buy college universities mobile number lists online.
Digital Signatures
This section will focus on digital signatures. It is the second cryptographic primitive (along with hash functions) that we need to build blocks for cryptocurrency discussion. Digital signatures are supposed to be digital analogs to handwritten signatures on paper. Two properties are required for digital signatures to be analogous to handwritten signatures. First, you are the only person who can sign your signature. However, anyone can see it and verify it is valid. We want your signature to be attached to a specific document. This will ensure that you cannot use it to signify your endorsement or agreement to another document. This property is similar to ensuring that someone can’t take your handwritten signature and cut it off one document, glue it on the bottom of another. Buy college universities mobile number lists online.
This is how we can build it digitally using cryptography. Let’s first make the intuitive discussion a little more concrete. This will enable us to think more clearly about digital signature schemes, and their security properties.
Let’s now look at the two requirements for a digital signature system in greater detail. The first property is simple — valid signatures must be verified. If someone attempts to validate my signature using my secret key, sk, on the same message, then it must be valid. This property is essential for signatures to work. Buy college universities mobile number lists online.
Unforgeability. It is computationally impossible to forge signatures. An adversary who has access to your public key can see signatures on other messages. However, he cannot forge your signature on a message for which he hasn’t seen your signature. This property of unforgeability is usually formalized by a game we play with an opponent. Cryptographic security proofs often make use of games. Buy college universities mobile number lists online.
There is an opponent who claims he can forge signatures. A challenger will then test that claim. We use generateKeys to generate a secret signing and public verification key. The challenger gets the secret key, while the adversary receives the public key. The adversary has access to only information that is public. His mission is to create a message. The secret key is known by the challenger. He can then sign.
The game’s setup matches the real world, according to intuition. An attacker could likely see the signatures of their victim on many documents. If the attacker is clever, the attacker might even be able to manipulate the victim into signing harmless-looking documents.
College Universities telephone number lists
This is how we will model it in our game. We’ll allow the attacker sign on documents of his choosing for as long and as possible. We would let the attacker try 1,000,000 guesses to give you an idea of what we mean when we say “possible number of guesses”.

College Universities telephone number lists
80
2 .
Guesses are not two-guesses
After the attacker has verified that there are enough signatures, the attacker will pick a message M to attempt to forge signatures. Only one restriction applies to M: it must contain a message that the attacker has never seen before. (As attackers can send back signatures he’s already received! To verify that the attacker’s signature is valid, the challenger uses the verifyalgorithm. The attacker wins the game if it succeeds in verifying.
Asymptoticly, the attacker can try as many guesses as is a polynomial function the key size. However, the attacker cannot attempt more than that (e.g. The attacker cannot attempt an infinite number of guesses.
We believe that the signature scheme cannot be forgeable if and only when, regardless of the algorithm used by the adversary, the chance of him successfully forging a message in practice is very small. Buy college universities telephone number lists online.
Practical concerns. There are many practical aspects that must be done to make the algorithmic idea a digital signature mechanism that is feasible to implement in practice. Many signature algorithms, including the one used in Bitcoin, are random and therefore require a source of randomness. This is an important aspect that cannot be understated. Bad randomness can make otherwise secure algorithms insecure.
The message size is another concern. The message size is a limitation in practice. Real schemes will only accept bit strings with a limited length. This limitation can be circumvented by signing the hash of the message instead of the message. We can sign any message with a cryptographic hash function that outputs 256 bits. As long as the signature scheme can sign 256 bit messages, we can also sign it. The hash function is not susceptible to collision, so it is safe to use the message digest as the message digest.
A hash pointer is another trick we’ll use. Signing a hashpointer covers or protects the entire structure, not just the hash-pointer. It also covers all the points in the chain. If you signed the hashpointer at the end a block chain, you would be digitally signing that block chain. Buy college universities telephone number lists online.
ECDSA. Now let’s get to the meat and potatoes. The Elliptic Curve Digital Signature Algorithm is a specific digital signature scheme used by Bitcoin. ECDSA, a U.S. government standard is an updated of the DSA algorithm that was adapted to use Ellipsic curves. These algorithms have been subject to extensive cryptographic analysis and are generally considered secure.
ECDSA is used by Bitcoin over the standard elliptic curve secp256k1 which is believed to provide 128 bits security. Buy college universities telephone number lists online. This means that it is nearly as difficult to break this algorithm than performing 2128 symmetric key cryptographic operations, such as calling a hash function. This curve is published but is not used by any other applications than Bitcoin. Other applications that use ECDSA, such as key exchange in TLS to secure web browsing, typically use the “secp256r1”. This is a quirk in Bitcoin. Satoshi chose this curve when the system was first described. It is difficult to change.
College Universities mobile number database
Because ECDSA is a complex math system, we won’t get into the details. Understanding it isn’t necessary for any of our other content. For more information, see the section on further reading at the end. However, it might be helpful to get an idea of the different sizes of quantities.

College Universities mobile number database
ECDSA can only sign messages up to 256 bits in length, but this is not an issue: all messages are hashed before they can be signed.
ECDSA requires that you have a reliable source of randomness. Otherwise, your key could be lost. You can see that bad randomness is a problem when generating keys. Your key will not be secure. It’s an oddity of ECDSA3 to say that even if you use poor randomness, your key will still be secure.
This is an elliptic curve variant of DSA. It’s a common quirk in DSA. Buy college universities mobile number database online.
Randomness is what you get when signing a signature using your perfectly good key. This will also leak your private key. Then it’s over. An adversary could forge your signature if your private key is leaked. It is important to use good randomness in practice. Using a poor source of randomness can lead to security problems.
This concludes our discussion on digital signatures as cryptographic primitives. We’ll be discussing some digital signature applications that can be used to build cryptocurrencies in the next section.
Sidebar: Cryptocurrencies and encryption. We’re sorry that you’ve been waiting to see which algorithm is used in Bitcoin. Bitcoin does not have encryption. This is because there is nothing that needs to be encrypted. We’ll explain why. Modern cryptography has made encryption possible in many ways. Many of them, like commitment schemes, involve hiding data in some way but they are different from encryption. Buy college universities mobile number database online.
Public Keys as Identities
Let’s take a look at a neat trick that comes with digital signatures. It is possible to use a public key (one of the public verification keys in a digital signature scheme) to identify a person or actor within a system. You can consider a message that has a signature that is valid under a public key, called pk, as pkis. A public key can be thought of as an actor or party that can sign statements. The public key can be viewed as an identity. To speak for the identity pk someone must have the secret key, sk. Buy college universities mobile number database online.
A consequence of treating public keys as identities is that you can make a new identity whenever you want — you simply create a new fresh key pair, sk andpk,via the generateKeysoperation in our digital signature scheme. You can pkis the public identity you want to use and skis the secret key you only know. This allows you to speak on behalf of the identity identity pk. To verify that a message is coming from you, you will need to (1) check that pkindeed hashes your identity and (2) that the message validates under public key pk.
Your public key pk will look random by default. Nobody can see your real identity.4But you can create a new identity that looks random and is like a face in a crowd. This is something only you can do.
College Universities contact number database
This is the concept of decentralized identification management. You don’t need to register to a system from a central authority. Instead of having to go to a central authority, you can register yourself. You don’t have to be given a username.

College Universities contact number database
You should be aware that statements made using this identity can leak information which could allow you to link pkto your real identity. This will be discussed in detail. Tell someone you are going to use a specific name. You can create a new identity at any time. No problem if you prefer to go by five different names. You can create five identities. You can create a new identity to remain anonymous for a short time, then discard it. These are all possible thanks to decentralized identity management.
This is how Bitcoin actually manages identity. In Bitcoin jargon, these identities are known as addresses. The term address is often used in connection with Bitcoin and other cryptocurrencies. It’s a hash of the public key. It is an identity someone created out of thin air as part of the decentralized identity management system. Buy college universities contact number database online.
Sidebar. It may seem counterintuitive to think that you can create an identity without having to go through a central authority. Sidebar. If someone else is lucky enough to generate the same key, can they steal your bitcoins or get your identity?
Answer: The probability that someone else will generate the same 256-bit key that you do is so low that we don’t need to worry about it in real life. It is almost certain that it won’t happen.
Generally, contrary to the belief that probabilistic systems can be unpredictable and difficult to understand, the theory of statistics can help us quantify the likelihood of the events we are interested in and to make confident predictions about their behavior. Buy college universities contact number database online.
There is a subtle distinction: The probabilistic guarantee can only be given if keys are generated randomly. Real systems often have weak points in the generation of randomness. The theoretical guarantees will not apply if two computers are using the same source or predictable randomness. It is important to generate keys from a reliable source of randomness in order to guarantee that the theoretical guarantees are met. Buy college universities contact number database online.
It may seem that decentralized identity management allows for privacy and anonymity at first glance. You can create an anonymous identity by yourself and not reveal your real-world identity. It’s not as simple as that. The identity you create over time will make a series statements. These statements are visible to the public and they can infer that the identity owner has performed a specific set of actions. These actions can be used to help them connect the dots and infer your real-world identity. These observations can be linked over time and inferred by an observer to make inferences such as “Gee, this is Joe.” This person could be Joe.
This means that in Bitcoin, you don’t have to register or reveal your real identity. However, the pattern of your behaviour might be used to identify you. This is the central privacy issue in a cryptocurrency such as Bitcoin and we will devote Chapter 6 to it. Buy college universities contact number database online.
A simple cryptocurrency
Let’s now move on to cryptography and cryptocurrencies. It will pay to eat our cryptographic fruits and vegetables. We’ll slowly see how they fit together and explain why cryptographic operations such as digital signatures and hash functions are so useful. This section will focus on two simple cryptocurrencies. It will take a lot of time to explain the implications of Bitcoin’s operation.
College Universities cellular phone number database
GoofyCoin
GoofyCoin is the first, and it is the most basic cryptocurrency we know. GoofyCoin has only two rules. First, GoofyCoin allows a designated entity (Goofy) to create new coins at any time he wishes. These coins are his.

College Universities cellular phone number database
Goofy creates a unique ID uniqueCoinID that he has never created before. He then constructs the string “CreateCoin[uniqueCoinID]”. The digital signature of the string is then calculated using his secret signing key. Together with Goofy’s signature the string is a coin. Anybody can verify that the coin has Goofy’s valid signature on a CreateCoin statement. It is therefore valid.
GoofyCoin’s second rule is that anyone who owns a coin may transfer it to another person. It’s not as simple as sending the data structure of a coin to the recipient. It involves cryptographic operations.
Let’s suppose that Goofy wishes to send a coin he made to Alice. He creates a new sentence that reads “Pay this to Alice”, where “this” refers to the coin. As we have seen, identities are just public keys. “Alice” is Alice’s public secret. Goofy then signs the string that represents the statement. Goofy, who is the original owner of the coin, must sign all transactions that involve the coin. Alice is the owner of the coin once the data structure that represents Goofy’s signed transaction exists. Because she has the data structure and Goofy’s signature, she can show anyone she owns it. It also points to a valid, owned coin by Goofy. The system is clear that coins can be valid and owned. Buy college universities phone number database online.
Alice can then spend the coin in her turn once she has it. She creates a statement saying, “Pay this currency to Bob’s public keys”, where “this” refers to the hash pointer to her coin. Alice then signs the statement. Anybody can confirm that Bob is the owner of this coin if presented with it. They would then follow the chain of hash points back to the coin’s origin and verify that the rightful owner signed a statement saying “Pay this coin to [new owners]”.
The rules of GoofyCoin can be summarized as follows:
Goofy can make new coins by signing a statement stating that he is making a coin with a unique ID. Buy college universities phone number database online.
Anyone who owns a coin may sign a statement saying “Pass it on to X” (where the coin is identified as a public secret).
Anybody can verify the authenticity of a coin by following the hash pointer chain back to its creation by Goofy and verifying each signature.
There is a security issue with GoofyCoin. Let’s suppose Alice gave her coin to Bob. She sent Bob a signed statement, but she didn’t tell anyone. Chuck could also receive the same coin through another signed statement. Chuck would think it was a valid transaction and he is now the owner. Chuck and Bob would each have valid claims to the coin’s ownership. This is known as a double-spending attack. Alice is spending the exact same coin twice. We intuitively know that coins don’t work this way. Buy college universities phone number database online.
Double-spending attacks are a key problem that every cryptocurrency must solve. GoofyCoin doesn’t solve double-spending attacks and is therefore not secure. GoofyCoin’s mechanism for transferring coins to and from the bank is very similar to Bitcoin. However, it is not secure enough to be considered a cryptocurrency.
College Universities cellular phone number lists
ScroogeCoin
We’ll create another cryptocurrency called ScroogeCoin to solve double-spending. ScroogeCoin is based on GoofyCoin but has more complex data structures.

College Universities cellular phone number lists
First, Scrooge, a designated entity, publishes an append onlyledger that contains the history of all transactions that have occurred. This append-only property guarantees that all data stored in this ledger will be preserved forever. We can defend against double-spending if the ledger truly is append-only by requiring that all transactions be written to the ledger before being accepted. This will make it publicly visible if coins have been sent to another owner.
Scrooge will digitally sign a block chain, which is the data structure we talked about before, to implement append-only functionality. It’s a series data blocks with one transaction each. In practice, however, multiple transactions can be placed in the same block as Bitcoin. Each block contains the ID of the transaction, its contents and a hash reference to the previous block. Scrooge digitally signs this last hash pointer. This binds all data in the entire structure and publishes it along with the block chains. Buy college universities cellular phone number lists online.
ScroogeCoin only considers transactions if they are in the block chain signed Scrooge. Anyone can check the signature of Scrooge on the block that a transaction appears in to verify that it was authorized by Scrooge. Scrooge won’t endorse any transaction that double-spends an already spent coin.
Why is it necessary to have Scrooge sign every block and create a block chain with hash pointsers? This protects the append only property. Scrooge can add or remove transactions to the history or modify an existing transaction. This will impact all blocks that are affected by the hash pointsers. The change will be easily detected and caught if someone is keeping track of the latest Scrooge hash pointer. If Scrooge had signed each block individually, it would be difficult to track every signature Scrooge issued. It is very simple for two people to confirm that they have seen the same transaction history signed by Scrooge using a block chain. Buy college universities cellular phone number lists online.
In ScroogeCoin, there are two sorts of exchanges. The primary kind is CreateCoins, which is very much like the activity Goofy could do in GoofyCoin that makes another coin. With ScroogeCoin, we’ll stretch out the semantics a piece to permit different coins to be made in one exchange.
A CreateCoins exchange is generally substantial by definition in the event that it is endorsed by Scrooge. We won’t stress over when Scrooge is qualified for make coins or the number of, very much as we didn’t stress in GoofyCoin over how Goofy is picked as the element permitted to make coins. Buy college universities cellular phone number lists online.
The second sort of exchange is PayCoins. It consumes a few coins, that is to say, obliterates them, and makes new coins of a similar complete worth. The new coins could have a place with various individuals (public keys). This exchange must be endorsed by every individual who’s paying in a coin. So assuming you’re the proprietor of one of the coins that will be consumed in this exchange, then, at that point, you really want to carefully sign the exchange to say that you’re truly good with spending this coin.
The standards of ScroogeCoin say that PayCoins exchange is legitimate assuming four things are valid:
The consumed coins are legitimate, that is to say, they truly were made in past exchanges. Buy college universities cellular phone number lists online.
The consumed coins were not currently consumed in some past exchange. That will be, that this isn’t a double‐spend.
The complete worth of the coins that emerge from this exchange is equivalent to the absolute worth of the coins that went in. That is, no one but Scrooge can make new worth.
The exchange is truly endorsed by the proprietors of the consumed coins in general.
College Universities phone number directory
In the event that those conditions are met, this PayCoins exchange is substantial and Scrooge will acknowledge it. He’ll compose it into the set of experiences by adding it to the block chain, after which everybody can see that this exchange has occurred. It is just right now that the members can acknowledge that the exchange has really happened. Until it is distributed, it very well may be seized by a douple‐spending exchange regardless of whether it is generally legitimate by the initial three circumstances.

College Universities cellular phone number directory
Coins in this framework are permanent — they are rarely different, partitioned, or joined. Each coin is made, once, in one exchange and later consumed in another exchange. Be that as it may, we can get a similar impact as having the option to partition or join coins by utilizing exchanges. For instance, to partition a coin, Alice make another exchange that consumes that one coin, and afterward delivers two new coins of a similar all out esteem. Those two new coins could be appointed back to her. So despite the fact that coins are changeless in this framework, it has all the adaptability of a framework that didn’t have unchanging coins.
Presently, we come to the center issue with ScroogeCoin. ScroogeCoin will work as in individuals can see which coins are legitimate. It forestalls double‐spending, in light of the fact that everybody can investigate the block chain and see that the exchanges are all substantial and that each coin is consumed just a single time. In any case, the issue is Scrooge — he has an excessive amount of impact. He can’t make counterfeit exchanges, since he can’t produce others’ marks. However, he could prevent supporting exchanges from certain clients, denying them administration and making their coins unspendable. In the event that Scrooge is voracious (as his animation namesake recommends) he could decline to distribute exchanges except if they move some ordered exchange charge to him. Miser can likewise obviously make however many new coins for himself as he needs. Or on the other hand Scrooge could get exhausted of the entire framework and quit refreshing the block chain totally. Buy college universities phone number directory online.
The issue here is centralization. Despite the fact that Scrooge is content with this framework, we, as clients of it, probably won’t be. While ScroogeCoin might appear to be a ridiculous proposition, a significant part of the early examination on cryptosystems expected there would for sure be some focal confided in power, ordinarily alluded to as a bank.After all, most real‐world monetary standards really do have a confided in backer (normally an administration mint) liable for making cash and figuring out which notes are legitimate. In any case, digital currencies with a focal authority to a great extent neglected to take off by and by. There are many purposes behind this, yet looking back apparently it’s challenging to get individuals to acknowledge a digital currency with an incorporated power. Buy college universities phone number directory online.
Thusly, the focal specialized challenge that we really want to tackle to develop ScroogeCoin and make a serviceable framework is: can we descroogify the framework? That is, might we at any point dispose of that brought together Scrooge figure? Might we at any point have a digital currency that works like ScroogeCoin in numerous ways, yet has no focal confided in power?
That’s what to do, we really want to sort out how all clients can concur upon a solitary distributed block chain as the historical backdrop of which exchanges have occurred. They should all settle on which exchanges are substantial, and which exchanges have really happened. Buy college universities phone number directory online. They likewise should have the option to dole out IDs to things in a decentralized manner. At long last, the printing of new coins should be controlled in a decentralized manner. In the event that we can take care of those issues, then we can fabricate a cash that would be like ScroogeCoin yet without a unified party. This would be a framework particularly like Bitcoin, as a matter of fact.
Top College Universities phone number lists
How Bitcoin Achieves Decentralization
In this section, we will examine decentralization in Bitcoin. In the primary part we took a gander at the crypto essentials that underlie Bitcoin and we finished with a basic money that we called ScroogeCoin. ScroogeCoin accomplishes a ton of what we need in a ledger‐based digital money, however it makes them glare issue — it depends upon the concentrated power called Scrooge.

Top College Universities phone number lists
We finished with the subject of how to decentralize, or de‐Scrooge‐ify, this cash, and addressing that question will be the focal point of this section.
As you read through this part, observe that the component through which Bitcoin accomplishes decentralization isn’t simply specialized, however it’s a mix of specialized strategies and cunning motivator designing. Toward the finish of this section you ought to have a great appreciation for how this decentralization occurs, and all the more by and large the way in which Bitcoin works and why it is secure. Buy top college universities phone number lists online.
Centralization versus Decentralization
Decentralization is a significant idea that isn’t novel to Bitcoin. The thought of contending ideal models of centralization versus decentralization emerges in a wide range of computerized advancements. To best comprehend how it works out in Bitcoin, it is valuable to grasp the focal struggle — the pressure between these two ideal models — in various different settings.
From one viewpoint we have the Internet, a broadly decentralized framework that has generally rivaled and beaten “walled‐garden” choices like AOL’s and CompuServe’s data administrations. Then there’s email, which at its center is a decentralized framework in light of the Simple Mail Transfer Protocol (SMTP), an open norm. While it has contest from exclusive informing frameworks like Facebook or LinkedIn mail, email has figured out how to stay the default for person‐to‐person correspondence on the web. On account of texting and text informing, we have a crossover model that can’t be completely portrayed as brought together or decentralized. Buy top college universities phone number lists online.
At last there’s person to person communication: in spite of various deliberate endeavors by specialists, engineers and business people to make options in contrast to the prevailing concentrated model, unified frameworks like Facebook LinkedIn actually rule this space. As a matter of fact, this contention long originates before the computerized period and we see a comparable battle between the two models throughout the entire existence of communication, radio, TV, and film.
Decentralization isn’t win big or bust; practically no framework is absolutely decentralized or simply unified. For instance, email is in a general sense a decentralized framework in view of a normalized convention, SMTP, and anybody who wishes can work their very own email server. However, what has occurred in the market is that few concentrated webmail suppliers have become predominant. Additionally, while the Bitcoin convention is decentralized, administrations like Bitcoin trades, where you can change over. Buy top college universities phone number lists online.
Bitcoin into different monetary standards, and wallet programming, or programming that permits individuals to deal with their bitcoins might be unified or decentralized to changing degrees.
In view of this, how about we separate the subject of how the Bitcoin convention accomplishes decentralization into five additional particular inquiries:
Who keeps up with the record of exchanges?
Who has authority over which exchanges are legitimate?
Who makes new bitcoins?
Who decides how the guidelines of the framework change?
How do bitcoins obtain trade esteem?
The initial three inquiries mirror the specialized subtleties of the Bitcoin convention, and these inquiries will be the focal point of this part.
Best College Universities phone number database
Various parts of Bitcoin fall on various focuses on the centralization/decentralization range. The peer‐to‐peer network is near simply decentralized since anyone can run a Bitcoin hub and there’s a genuinely low hindrance to section.

Best College Universities cellular phone number database
You can go on the web and effectively download a Bitcoin client and run a hub on your PC or your PC. At present there are a few thousand such hubs. Bitcoin mining, which we’ll concentrate on later in this part, is in fact likewise open to anybody, yet it requires an exceptionally high capital expense. Due to this there has been a serious level of centralization, or a convergence of force, in the Bitcoin mining biological system.
Numerous in the Bitcoin people group consider this to be very unwanted. A third viewpoint is updates to the product that Bitcoin hubs run, and this has a course on how and when the principles of the framework change. One can envision that there are various interoperable executions of the convention, likewise with email. However, practically speaking, most hubs run the reference execution, and its designers are confided in by the local area and have a ton of force. Buy best college universities phone number database online.
Appropriated agreement
We’ve examined, in a conventional way, centralization and decentralization. We should now look at decentralization in Bitcoin at a more specialized level. A key term that will come up all through this conversation is consensus,and specifically,distributed consensus.The key specialized issue to tackle in building a disseminated e‐cash framework is accomplishing circulated agreement. Naturally, you can consider our objective decentralizing ScroogeCoin, the speculative cash that we found in the principal part.
Disseminated agreement has different applications, and it has been read up for a really long time in software engineering. The customary propelling application is unwavering quality in conveyed frameworks. Envision you’re responsible for the backend for an enormous long range informal communication organization like Facebook. Frameworks of this sort commonly have thousands or even great many servers, which together structure an enormous disseminated data set that records every one of the activities that occur in the framework. Each snippet of data should be kept on a few unique hubs in this backend, and the hubs should be in a state of harmony about the general condition of the framework. Buy best college universities phone number database online.
The ramifications of having a conveyed agreement convention reach a long ways past this customary application. Assuming we had such a convention, we could utilize it to construct a monstrous, dispersed key‐value store, that maps inconsistent keys, or names, to erratic qualities. A dispersed key‐value store, thus, would empower numerous applications. For instance, we could utilize it to fabricate a distributive space name framework, which is essentially a planning between human justifiable space names to IP addresses. We could construct a public key index, which is a planning between email locations (or another type of real‐world personality) to public keys. Buy best college universities phone number database online.
That is the instinct of what dispersed agreement is, however it is valuable to give a specialized definition as this will assist us with deciding if a given convention meets the necessities.
Appropriated agreement convention. There are nnodes that each have an information esteem. A portion of these nodesare defective or noxious. A disseminated agreement convention has the accompanying two properties:
It should end with all fair hubs in settlement on the worth
The worth absolute requirement been produced by a genuine hub
What’s the significance here with regards to Bitcoin? To comprehend how disseminated agreement could function in Bitcoin, recall that Bitcoin is a peer‐to‐peer framework. At the point when Alice needs to pay Bob, what she really does is communicated an exchange to all of the Bitcoin hubs that involve the peer‐to‐peer network.
Best College Universities contact number lists
As it turns out, you might have seen that Alice communicates the exchange to all the Bitcoin peer‐to‐peer hubs, yet Bob’s PC is no place in this image. Obviously conceivable Bob is running one of the hubs in the peer‐to‐peer network.

Top College Universities contact number lists
As a matter of fact, to be advised that this exchange did truth be told occur and that he got compensated, running a hub may be smart. By the by, there is no prerequisite that Bob be tuning in on the organization; running a hub isn’t required for Bob to get the assets. The bitcoins will be his whether he’s working a hub on the organization.
What precisely is it that the hubs should arrive at agreement on in the Bitcoin organization? Considering that different clients are communicating these exchanges to the organization, the hubs should settle on precisely which exchanges were communicated and the request in which these exchanges occurred. This will bring about a solitary, worldwide record for the framework. Review that in ScroogeCoin, for streamlining, we put exchanges into blocks. Essentially, in Bitcoin, we do agreement on a block‐by‐block premise. Buy best college universities contact number database online.
So at some random point, every one of the hubs in the peer‐to‐peer network have a record comprising of a succession of blocks, each containing a rundown of exchanges, that they’ve arrived at agreement on. Furthermore, every hub has a pool of exceptional exchanges that it has caught wind of yet have not yet been remembered for the block chain. For these exchanges, agreement has not yet occurred, thus by definition, every hub could have a marginally unique rendition of the extraordinary exchange pool. Practically speaking, this happens on the grounds that the peer‐to‐peer network is more than a little flawed, so a few hubs might have caught wind of an exchange that different hubs have not found out about.
How precisely do hubs come to agreement on a block? One method for doing this: at customary spans, say like clockwork, each hub in the framework proposes its own exceptional exchange pool to be the following block. Then, at that point, the hubs execute some agreement convention, where every hub’s feedback is its own proposed block. Presently, a few hubs might be pernicious and placed invalid exchanges into their blocks, however we could expect that different hubs will tell the truth. On the off chance that the agreement convention succeeds, a legitimate block will be chosen as the result. Buy best college universities contact number lists online.
Regardless of whether the chose block was proposed by just a single hub, it’s a legitimate result as long as the block is substantial. Presently there might be some legitimate exceptional exchange that didn’t get remembered for the block, however this isn’t an issue. In the event that some exchange some way or another didn’t make it into this specific block, it could simply pause and get into the following block.
The methodology in the past section has a few likenesses to how Bitcoin functions, yet it’s not exactly the way that it works. There are various specialized issues with this methodology. Right off the bat, agreement overall is a difficult issue since hubs could crash or be by and large noxious. Besides, and explicitly in the Bitcoin setting, the organization is profoundly flawed. It’s a peer‐to‐peer framework, and not all sets of hubs are associated with one another. There could be flaws in the organization due to unfortunate Internet network for instance, and subsequently running an agreement convention in which all hubs should partake isn’t exactly imaginable. At long last, there’s a ton of dormancy in the framework since it’s circulated all around the Internet.

Best College Universities cellular phone number database online
