California Database Lists: Best CA Data Solutions
The #1 site to find California Database Lists and accurate B2B & B2C email lists. Emailproleads.com provides verified contact information for people in your target industry. It has never been easier to purchase an email list with good information that will allow you to make real connections. These databases will help you make more sales and target your audience. You can buy pre-made mailing lists or build your marketing strategy with our online list-builder tool. Find new business contacts online today!
Just $199.00 for the entire Lists
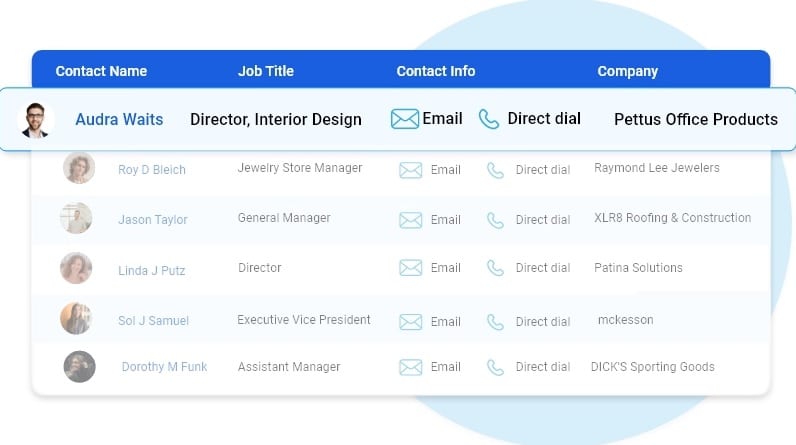
Customize your database with data segmentation
- Job Titles
- Job Function
- Company Size
- Revenue Size
- SIC Codes
- NAICS Codes
- Geographics
- Technology
- And more...

Free samples of California Database Lists
We provide free samples of our ready to use California Database Lists. Download the samples to verify the data before you make the purchase.

Human Verified California Database Lists
The data is subject to a seven-tier verification process, including artificial intelligence, manual quality control, and an opt-in process.
Best California Database Lists
Highlights of our California Database Lists
First Name
Last Name
Phone Number
Address
City
State
County
Zip
Age
Income
Home Owner
Married
Property
Networth
Household
Cradit Rating
Dwelling Type
Political
Donor
Ethnicity
Language Spoken
Email
Latitude
Longitude
Timezone
Presence of children
Gender
DOB
Birth Date Occupation
Presence Of Credit Card
Investment Stock Securities
Investments Real Estate
Investing Finance Grouping
Investments Foreign
Investment Estimated
Residential Properties Owned
Traveler
Pets
Cats
Dogs
Health
Institution Contributor
Donates by Mail
Veteranin Household
Heavy Business
Travelers
High Tech Leader
Smoker
Mail Order Buyer
Online Purchasing Indicator
Environmental Issues Charitable Donation
International Aid Charitable Donation
Home Swimming Pool
Look at what our customers want to share





FAQ
Our email list is divided into three categories: regions, industries and job functions. Regional email can help businesses target consumers or businesses in specific areas. California Database Lists broken down by industry help optimize your advertising efforts. If you’re marketing to a niche buyer, then our email lists filtered by job function can be incredibly helpful.
Ethically-sourced and robust database of over 1 Billion+ unique email addresses
Our B2B and B2C data list covers over 100+ countries including APAC and EMEA with most sought after industries including Automotive, Banking & Financial services, Manufacturing, Technology, Telecommunications.
In general, once we’ve received your request for data, it takes 24 hours to first compile your specific data and you’ll receive the data within 24 hours of your initial order.
Our data standards are extremely high. We pride ourselves on providing 97% accurate California Database Lists, and we’ll provide you with replacement data for all information that doesn’t meet your standards our expectations.
We pride ourselves on providing customers with high quality data. Our California Database Database and mailing lists are updated semi-annually conforming to all requirements set by the Direct Marketing Association and comply with CAN-SPAM.
California Database Lists
Emailproleads.com is all about bringing people together. We have the information you need, whether you are looking for a physician, executive, or California Database Lists. So that your next direct marketing campaign can be successful, you can buy sales leads and possible contacts that fit your business. Our clients receive premium data such as email addresses, telephone numbers, postal addresses, and many other details. Our business is to provide high-quality, human-verified contact list downloads that you can access within minutes of purchasing. Our CRM-ready data product is available to clients. It contains all the information you need to email, call, or mail potential leads. You can purchase contact lists by industry, job, or department to help you target key decision-makers in your business.
If you’re planning to run targeted marketing campaigns to promote your products, solutions, or services to your database, you’re at the right spot. Emailproleads dependable, reliable, trustworthy, and precise California Database List lets you connect with key decision-makers, C-level executives, and professionals from various other regions of the country. The list provides complete access to all marketing data that will allow you to reach the people you want to contact via email, phone, or direct mailing.

Our pre-verified, sign-up Email marketing list provides you with an additional advantage to your networking and marketing efforts. Our database was specifically designed to fit your needs to effectively connect with a particular prospective customer by sending them customized messages. We have a dedicated group of data specialists who help you to personalize the data according to your requirements for various market movements and boost conversion without trouble.
We gathered and classified the contact details of prominent industries and professionals like email numbers, phone numbers, mailing addresses, faxes, etc. We are utilizing the most advanced technology. We use trusted resources like B2B directories and Yellow Pages; Government records surveys to create an impressive high-quality Email database. Get the California Database today to turn every opportunity in the region into long-term clients.
Our precise Database Leads is sent in .csv and .xls format by email.
California Database Lists has many benefits:
Adestra recently conducted a survey to determine which marketing channel was the most effective return on investment (ROI). 68% of respondents rated email marketing as ‘excellent’ or ‘good.
California Database Leads can be cost-effective and accessible, which will bring in real revenue for businesses regardless of their budget. It is a great way for customers to stay informed about new offers and deals and a powerful way to keep prospects interested. The results are easy to track.
Segment your list and target it effectively:
Your customers may not be the same, so they should not receive the same messages. Segmentation can be used to provide context to your various customer types. This will ensure that your customers get a relevant and understandable message to their buying journey. This allows you to create personalized and tailored messages that address your customers’ needs, wants, and problems.
Segmenting your prospects list by ‘who’ and what is the best way to do so. What they’ve done refers to what they have done on your website. One prospect might have downloaded a brochure, while another person may have signed up for a particular offer. A good email marketing service will let you segment your list and automate your campaigns so that they can be sent to different customer types at the time that suits you best.
Almost everyone has an email account today. There will be over 4.1 billion people using email in 2021. This number is expected to rise to 4.6 billion by 2025. This trend means that every business should have an email marketing list.
California Database List is a highly effective digital marketing strategy with a high return on investment (ROI). Because millennials prefer email communications for business purposes, this is why.
How can businesses use email marketing to reach more clients and drive sales? Learn more.
California Database marketing has many benefits:
Businesses can market products and services by email to new clients, retain customers and encourage repeat visits. Database Lists marketing can be a great tool for any business.
High Conversions
DMA reports that email marketing has a $42 average return per $1. Email marketing is a great marketing strategy to reach more people and drive sales if you launch a promotion or sale.
You can send a client a special offer or a discount. California Database Lists can help automate your emails. To encourage customer activity, set up an automated workflow to send welcome, birthday, and re-engagement emails. You can also use abandoned cart emails to sell your products and services more effectively.
Brand Awareness
Database marketing allows businesses to reach qualified leads directly.
California Database will keep your brand in mind by sending emails to potential customers. Email marketing has a higher impact than social media posts because it is highly targeted and personalized.
Contrary to other channels, a business can send a lot of emails to large numbers of recipients at much lower costs.
Increase customer loyalty
One email per week is all it takes to establish unbreakable relationships with customers.
An email can be used to build customer loyalty, from lead-nurturing to conversion to retention and onboarding. A personalized email with tailored content can help businesses build strong customer relationships.
Tips for capturing email addresses
A business must have an email list to use email marketing. You will need a strategy to capture these email addresses.
California Database Lists will get your email campaigns off the ground with a bang!
We understand that reaching the right audience is crucial. Our data and campaign management tools can help you reach your goals and targets.
Emailproleads are a long-standing way to market products and services outside the business’s database. It also informs existing customers about new offerings and discounts for repeat customers.
We offer real-time statistics and advice for every campaign. You can also tap into the knowledge of our in-house teams to get the best data profile.
Your California Contact Database Lists marketing campaigns will feel effortless and still pack a punch. You can use various designs to highlight your products’ different benefits or help you write compelling sales copy.
Contact us today to order the Database marketing database to support your marketing. All data lists we offer, B2C and B2B, are available to help you promote your online presence.
We already have the database for your future customers. You will be one step closer when you purchase email lists from us.
Talk to our friendly team about how we can help you decide who should be included in your future email list.
The #1 site to find business leads and accurate California Database Leads. Emailproleads.com provides verified contact information for people in your target industry. It has never been easier to purchase an email list with good information that will allow you to make real connections. These databases will help you make more sales and target your audience. You can buy pre-made mailing lists or build your marketing strategy with our online list-builder tool. Find new business contacts online today!
